when choosing an overseas high-defense server in hong kong , users often ask three questions: which one is the "best"? which is the "best value for money"? which is the "cheapest"? "best" usually refers to the solution with the strongest protection capabilities, optimal bandwidth and latency, high service level agreement (sla) and timely technical support; "best" mostly refers to the solution that strikes a balance between performance, security and cost; "cheapest" focuses on basic protection and the lowest cost. this article starts from the perspective of actual deployment and emergency response to help readers make rational choices when renting high-defense servers , and provides a replicable fault emergency plan template.
overseas hong kong high-defense servers usually enjoy superior international/mainland links, low network latency and flexible export bandwidth, and are suitable for cross-border e-commerce, games, financial payments, media distribution and other businesses that are susceptible to ddos attacks or traffic surges. hong kong nodes have natural advantages in connecting mainland china and the international internet, which facilitates multi-node load balancing and cdn cooperation. when selecting, you need to pay attention to indicators such as ddos protection capabilities, peak bandwidth carrying capacity, and cleaning thresholds.
the key points of the evaluation include: 1) protection level (based on packets per second/traffic per second and cleaning capacity); 2) bandwidth and billing mode (fixed bandwidth vs. billing based on traffic); 3) network quality (packet loss, delay, peak stability); 4) sla and technical support timeliness; 5) hardware configuration (cpu, memory, storage io) and scalability; 6) compliance and filing requirements. based on these indicators, select a solution suitable for business peaks and budget, thereby striking a balance between cost and reliability.
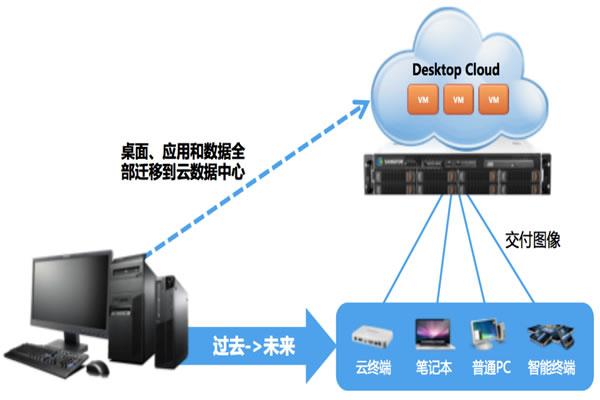
recommended architecture: while renting a high-defense server in hong kong, combine multiple availability zones (or multiple computer rooms) with load balancing and cdn nodes to achieve active traffic diversion. place cleaning equipment or cloud cleaning services at the entrance layer, and the backend uses a private network to connect to the application server and database. set flow limits and verification codes for important interfaces, and use web application firewall (waf) to filter common attacks to ensure that services are degraded rather than completely unavailable when an attack strikes.
at the host level, it is recommended to enable minimal system installation, close unnecessary ports, enable firewall policies and intrusion detection. enable key authentication, non-standard ports and ip whitelisting for the management port (ssh/rdp). enable centralized log collection and auditing, and remote backup of key logs. enable tls/https on the app and force the latest cipher suites. for databases and storage, use encryption and access isolation policies, and perform vulnerability scanning and patch management regularly.
build a unified monitoring system covering network, host, application and security. indicators include bandwidth traffic, number of connections, packet loss, delay, cpu/memory/disk io, error rate, etc. set up hierarchical alarms (information/warning/severe) and notify on-duty personnel through multiple channels (text messages, phone calls, work orders). develop regular inspection plans, backup verification and drill cycles to ensure rapid recovery in the event of a failure and to understand the root cause.
the following is a standardized fault emergency plan template: 1) initial identification: monitoring trigger or customer report - recording time/scope of impact/preliminary indicators; 2) rapid isolation: short-term isolation of abnormal traffic through black hole/traffic cleaning/routing adjustment; 3) graded response: s1 (emergency) assigns on-site/remote engineers and enable emergency calls; s2 (high) starts expansion or switches to standby machines; 4) recovery and verification: verify business functions, performance, and data integrity after cleaning; 5) root cause analysis: collect logs, capture packets, and audit configuration differences; 6) rectification and summary: update protection rules, processes, and drill plans, and form event reports.
common faults include: ddos attacks, link jitters and packet loss, hardware failures, configuration errors and application layer downtime. quick troubleshooting sequence: 1) confirm the scope and timeline of the impact; 2) view monitoring traffic curves and cleaning equipment status; 3) verify routing and bgp change records; 4) check host resources and error logs; 5) roll back recent configuration changes or deployments, and switch traffic to the backup computer room if necessary.
cost control strategies include combining cleaning and bandwidth on demand (basic protection + elastic cleaning), choosing protection levels for phased upgrades, and using prepaid and long-term contracts to obtain discounts. for small and medium-sized businesses, you can first choose the "best cost-effectiveness" solution to ensure basic sla and cleaning capabilities; for high-value businesses, it is recommended to directly purchase high-level sla and around-the-clock emergency support to avoid losses due to attacks that far exceed the cost of protection.

summary of key points: when selecting overseas high-defense servers in hong kong , measuring "best/best/cheapest" requires a combination of business value and risk tolerance; use multi-layer protection, redundant architecture and perfect monitoring when deploying; and prepare a practical failure emergency plan , and conduct regular drills and optimizations. recommended list: clarify attack tolerance, measure bandwidth peak, sign clear sla, deploy waf + cleaning, and establish a 24/7 duty and drill mechanism.
- Latest articles
- How Do Small And Medium-sized Enterprises Determine Which Cloud Server In Malaysia Is Good? Cost Control And Scalability Analysis
- Practical Comparison And Analysis Of The Difference In Seo Effects Between 20m And Higher Bandwidth In Taiwan’s Station Cluster
- How To Evaluate The Performance Advantages Of Singapore Dual Isp Vps In Multinational Business
- Sharing The Successful Experience Of Small And Medium-sized Enterprises Adopting Malaysian Cn2 To Improve Overseas User Coverage
- Actual Measurement And Optimization Suggestions Of Alibaba Cloud Server Latency And Throughput Performance In Singapore
- How To Choose A Us Server With Cn2 Solution And Deployment Tips Suitable For Your Enterprise
- Website Acceleration Tips Share How To Use Cdn And Load Balancing To Optimize The Us Www Server Access Experience
- U.s. Qualcomm High-defense Server Traffic Scheduling And Capacity Expansion Practical Case During E-commerce Promotion Period
- Detailed Explanation Of What Hong Kong’s Native Ip Ladder Is And Comparison Of Common Protocols And Encryption Methods
- Sniper 2 Vietnam Server Compatibility Problem Solving And Driver Optimization Tips
- Popular tags
-
Best Guide To Use Lightweight Native Ip In Alibaba Cloud Hong Kong
this article introduces you in detail the best guide to using alibaba cloud hong kong's lightweight native ip, including server configuration, real cases and usage skills. -
Sharing Of Practical Application Cases Of Native Hong Kong Ip In Cross-border Marketing
detailed evaluation and application: how to use native hong kong ip and hong kong servers to improve delivery accuracy, access speed and data compliance in cross-border marketing, including cost, performance and practical cases. -
Best Practices And Suggestions For Selecting High-defense Servers In Hong Kong
best practices and suggestions for selecting high-defense servers in hong kong, understand the advantages of high-defense servers, and how to choose a suitable service provider.